Documentation Index
Fetch the complete documentation index at: https://help.cryptolens.io/llms.txt
Use this file to discover all available pages before exploring further.
Idea
Normally, node-locking (aka machine code locking) works on a per-device basis. If the same end user frequently switches devices, a device-based license can be inconvenient because old devices may need to be deactivated before new devices can activate. One solution is floating licensing, where deactivations occur automatically. Another solution is to count users instead of devices. With per-user seat licensing, each activation represents a user seat. Instead of sending a device fingerprint asMachineCode, your application sends a stable user identifier, such as an SSO subject, Entra ID/Azure AD object ID, user principal name (UPN), email address, or an HMAC of one of those values. The license’s maximum number of machines then becomes the maximum number of user seats.
This works best when your application already knows who the user is through a trusted identity system, such as SSO or an enterprise directory. Cryptolens then enforces the number of users allowed to use the license; your identity provider remains responsible for login, password reset, multi-factor authentication, and account lifecycle.
When to use it
Use this pattern when you want one license key to allow a fixed number of named users, and the user’s device should not matter. For example, an enterprise customer might buy 25 seats, and each employee should consume one activation no matter how many approved workstations they use. Avoid this pattern for username/password login, customer account management, password reset, or retrieving all licenses that belong to a customer. Those are authentication and account-management flows, and Cryptolens has dedicated options for them:- User authentication gives an overview of the supported authentication approaches.
- User verification covers username/password flows using
UserAuth. - Customer secret helps when one customer has many licenses and should not need to remember every key.
- Customer portal and User Account Authentication let Cryptolens handle the customer account experience.
Implementation
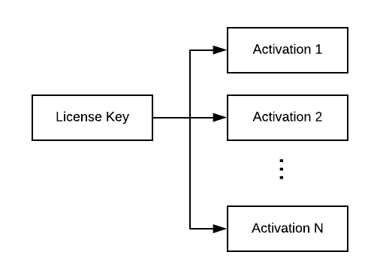
First, set the license’s maximum number of machines to the number of user seats you want to allow. Each uniqueMachineCode value consumes one activation, so a license with 25 maximum machines can represent 25 named users in this model.
Then choose a stable user identifier from your identity system:
- Prefer an immutable identifier, such as an SSO subject or directory object ID.
- A UPN or email address can work if it is stable in your environment.
- If you do not want to store the raw identifier in Cryptolens, store an HMAC or other deterministic pseudonymous value instead.
- Avoid display names and other values that can change or collide.
In enterprise environments, do not assume that a Windows, Active Directory, or Entra ID/Azure AD identifier is always available or configured consistently. Prefer an identifier from the authentication flow your application already trusts, such as an SSO subject or directory object ID. If you cannot reliably obtain a stable user identifier, use a dedicated authentication flow such as User verification, Customer portal, or Customer secret instead.
MachineCode identifies the user rather than the device.
MachineCode, Cryptolens treats it as the same activation. If a different user signs in, that user’s stable identifier consumes another activation until the license reaches its maximum number of machines.
As with any license verification flow, continue to check the license state that matters for your product, such as product ID, expiry date, blocked status, and feature flags. If you use signed responses or offline verification, apply the same signature and offline-fallback checks you use for regular key verification.
Legacy username/password variant
Earlier versions of this tutorial described a username/password variant that stored a password hash inMachineCode, stored the username in FriendlyName, and later checked the license with Key.GetKey. Treat that approach as legacy and avoid it for new integrations.
The issue is not that seat counting with activations is invalid; the issue is mixing licensing seat tracking with authentication. Password storage, password verification, password reset, user registration, account removal, and scoped permissions should be handled by the dedicated user-authentication flows instead.
If you need users to sign in with a username and password, use User verification or start from the User authentication overview. Those flows use the UserAuth methods and access-token permissions designed for login, registration, association, password changes, password reset, and user removal.
FAQ
How is this different from user account authentication?
User Account Authentication lets customers authenticate with their Cryptolens account so your application can retrieve the licenses associated with that customer. It is an authentication and account-access flow. Per-user seats using activations is a licensing model. It uses the activation list on a license key as the seat list, where each activation represents one user instead of one device.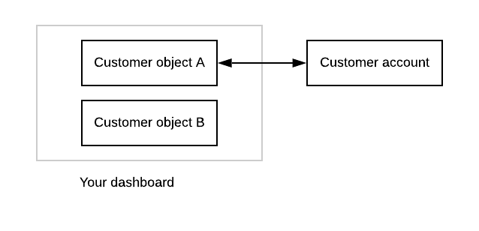
Can one user use multiple devices?
Yes. If your application sends the same stable user identifier asMachineCode on each device, that user consumes one activation.